Understanding Cybersecurity for Automotive ECUs: A Comprehensive Introduction
One of the primary obstacles confronting OEMs today is the realm of automotive cybersecurity. This challenge has intensified due to the significant rise in integrated
One of the primary obstacles confronting OEMs today is the realm of automotive cybersecurity. This challenge has intensified due to the significant rise in integrated

Colocation is an increasingly popular solution for enterprise-grade businesses that require robust, secure, and scalable IT infrastructure. In a colocation setup, companies lease space within

VMware ESXi is a powerful Type-1 hypervisor that enables virtualization, allowing multiple virtual machines (VMs) to run on a single physical server. While VMware ESXi

IP Address Spoofing is a technique used by attackers to mask their true identity by forging the source IP address in a data packet. By

Subnetting is a method of dividing an IP address space into smaller, manageable networks or subnets, each with a specific range of addresses. Understanding how

A Distributed Denial of Service (DDoS) attack is a cyberattack that overwhelms a targeted server, service, or network with a flood of internet traffic, rendering
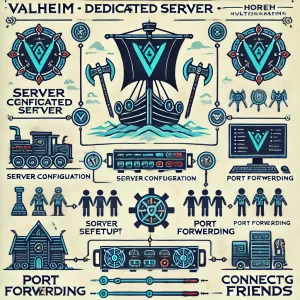
Playing Valheim on a dedicated server offers a smoother, lag-free experience, allowing you and your friends to explore the Norse-inspired world together without relying on

For small websites, choosing a Content Delivery Network (CDN) can make a big difference in speed, user experience, and SEO rankings. BunnyCDN and Quick.Cloud are

In today’s digital world, speed and reliability are crucial for providing the best user experience, regardless of where users are located. A Multi-CDN (Content Delivery
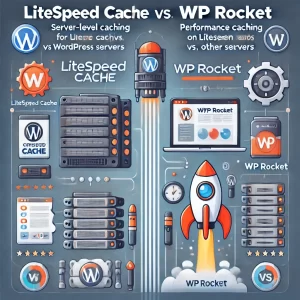
WordPress caching plugins play a crucial role in speeding up websites, enhancing user experience, and improving SEO. Two of the most popular caching plugins are